---
title: SharePoint Online & OneDrive Access Needs for MS Graph based live search
excerpt: >-
Use this guide to configure a per-user Microsoft Graph integration so
Moveworks can perform Live Search across SharePoint Online and OneDrive.
deprecated: false
hidden: true
metadata:
title: ''
description: ''
robots: index
next:
description: ''
---
Moveworks requires an **Azure App registration** (which creates an Enterprise application/service principal) to connect to Live Search for SharePoint & OneDrive. This connection will enable your users to connect to **both** SharePoint & OneDrive via a single connector.
## Content Types
**Indexing (SharePoint Online)**
1. Pages (modern site pages, classic wiki pages and classic publishing pages).
2. Documents stored in SharePoint document libraries (including common attachments).
3. Supported file formats: doc, docx, pdf, ppt, pptx, txt, html, aspx(pages)
**Live Search (SharePoint Online & OneDrive)**
1. On-demand results from the signed-in user’s accessible SharePoint sites/libraries and their OneDrive files/folders. It includes Pages, Documents, Lists etc.
2. Not indexed into the enterprise corpus; fetched at query time after user consent.
# Access Requirements
## Pre-requisites
Before you get started, make sure you have everything you need:
* **Admin roles**
* [**Global Admin**](https://learn.microsoft.com/en-us/microsoft-365/admin/add-users/about-admin-roles?view=o365-worldwide#commonly-used-microsoft-365-admin-center-roles:~:text=and%20manage%20auditing-,Global%20admin,-Giving%20too%20many) to create the app registration and grant admin consent for Graph scopes.
* [**SharePoint Admin**](https://learn.microsoft.com/en-us/microsoft-365/admin/add-users/about-admin-roles?view=o365-worldwide#commonly-used-microsoft-365-admin-center-roles:~:text=Monitor%20service%20health-,SharePoint%20administrator,-Assign%20the%20SharePoint) to confirm tenant domains and validate that SharePoint/OneDrive content is accessible as expected.
## Detailed Instructions to set up a new Enterprise Application registration
You can find Microsoft’s documentation on setting up this Application here: [https://learn.microsoft.com/en-us/graph/auth-register-app-v2](https://learn.microsoft.com/en-us/graph/auth-register-app-v2)
The streamlined steps are described below, starting with creating a new Registration in Azure ([portal.azure.com](http://portal.azure.com)).
### 1. Register a new App
1. Sign in to the [Azure portal](https://portal.azure.com/).
2. Select **Microsoft Entra ID > Manage > App registrations > New registration**.
3. On the Register an application page, register an app with the following details
| Field | Value |
| :---------------------- | :------------------------------------------------------------- |
| Name | `Moveworks - Live Search` |
| Supported account types | Accounts in this organizational directory only (Single tenant) |
| Redirect URI | Web -> `https://{org}.moveworks.com/auth/oauthCallback` |
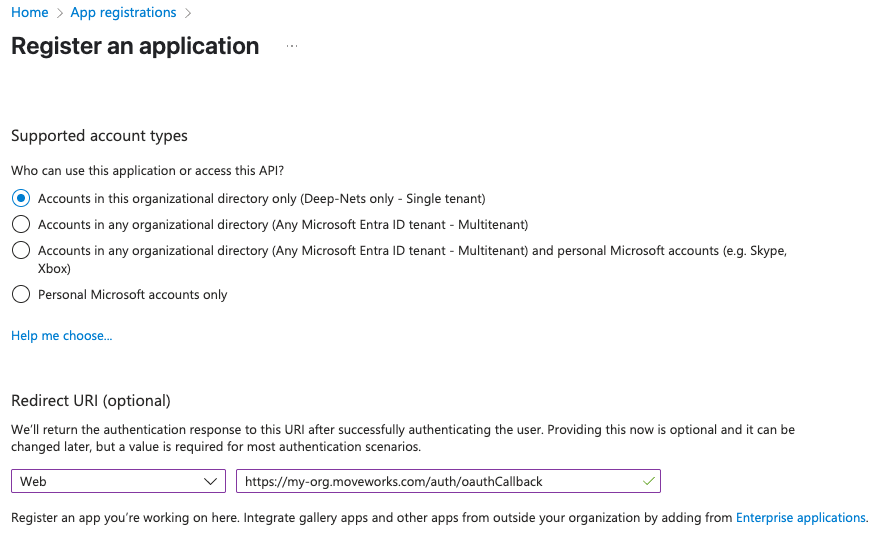
> Note:
>
> Ensure the Redirect URI is a **Web** application, and when specifying the Redirect URI, include your specific sub-domain for MyMoveworks.
>
> `https://{org}.moveworks.com/auth/oauthCallback` — for US orgs
>
> Make sure to replace the `{org}` with your specific sub-domain.
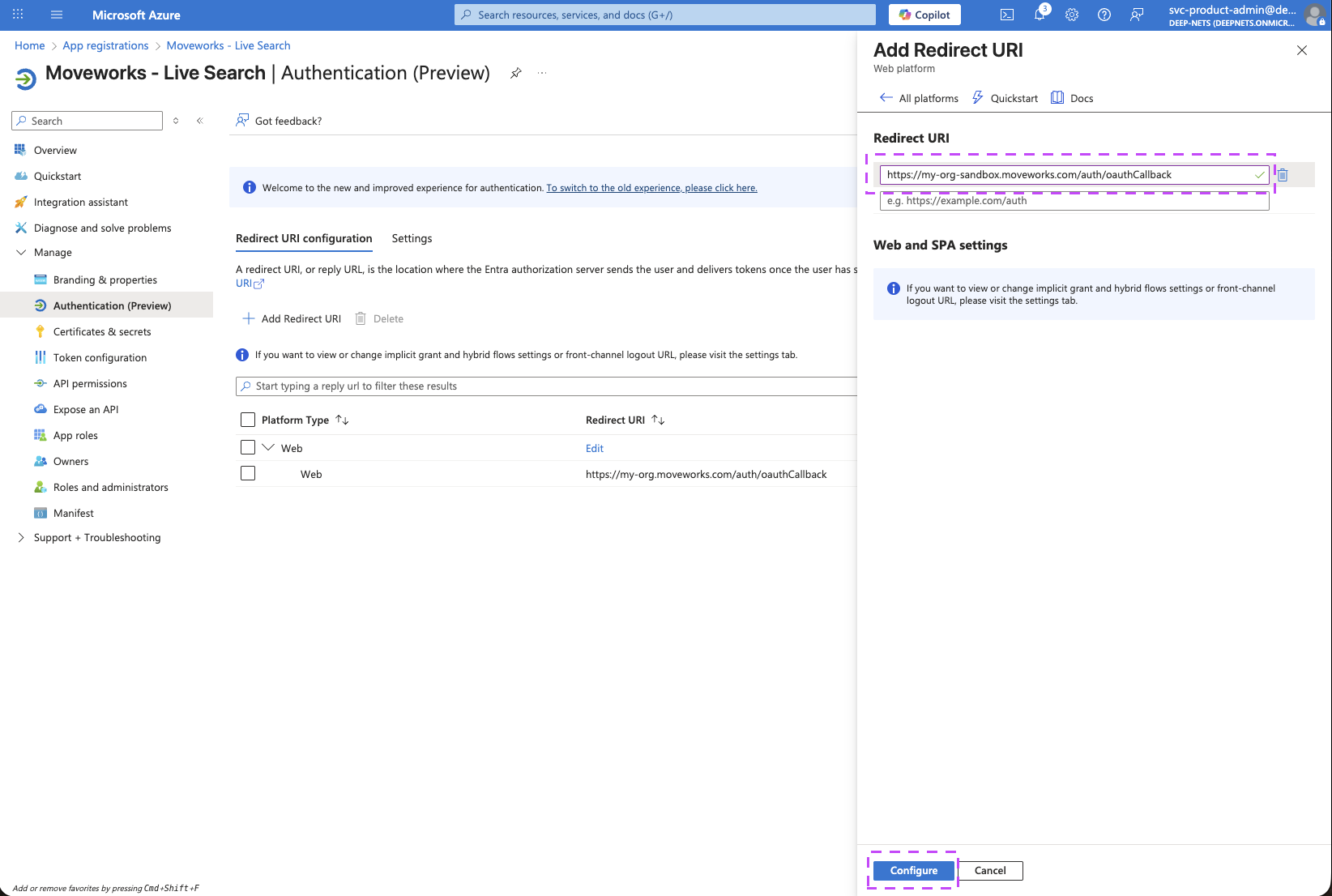
If you have a sandbox MyMoveworks environment, please configure an additional URL for that too:
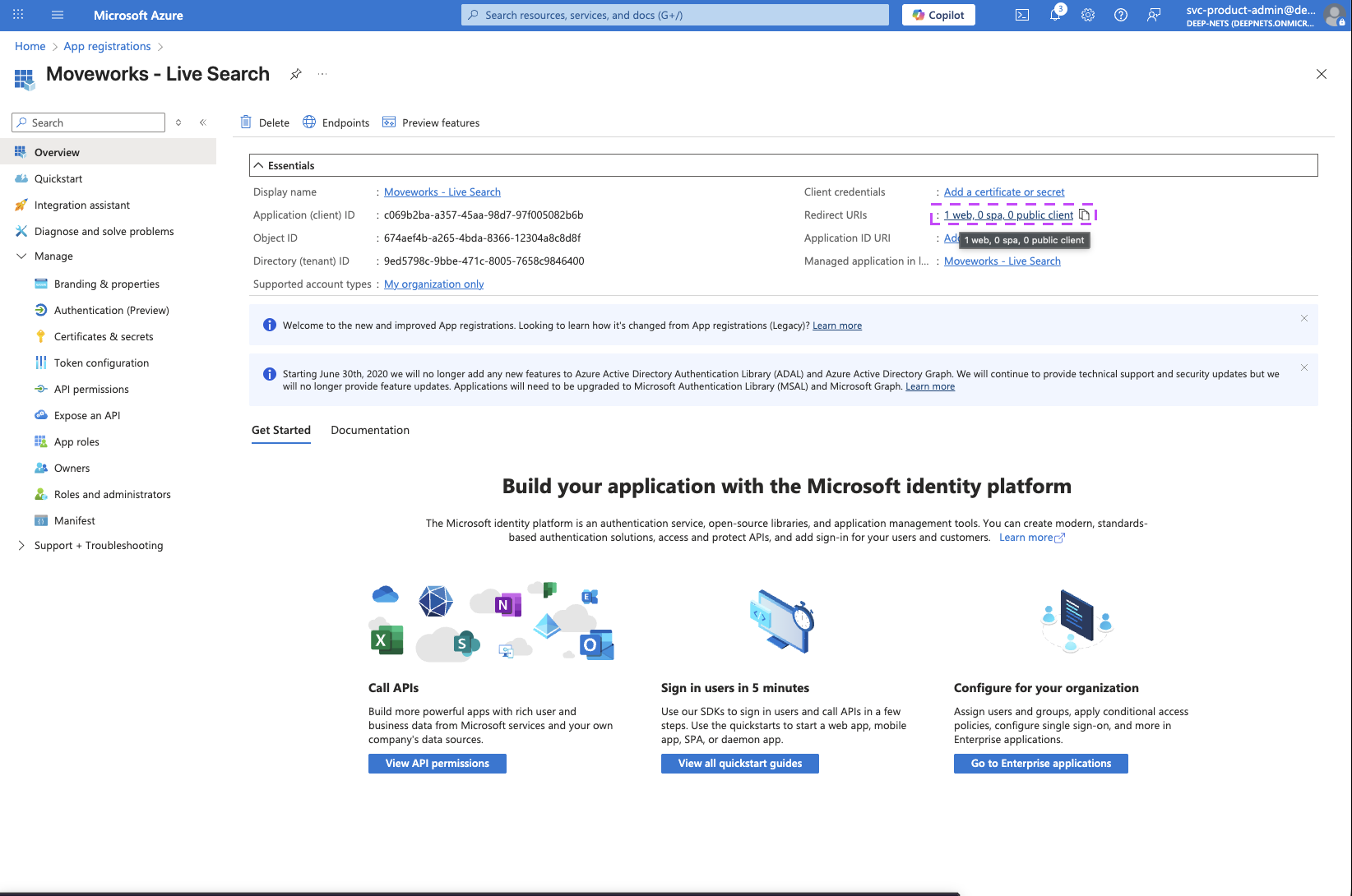
1. On the Home page of the Application you just created, click on the Redirect URIs link
2. On the page that opens, click on the **Add Redirect URI** button to add an additional URI
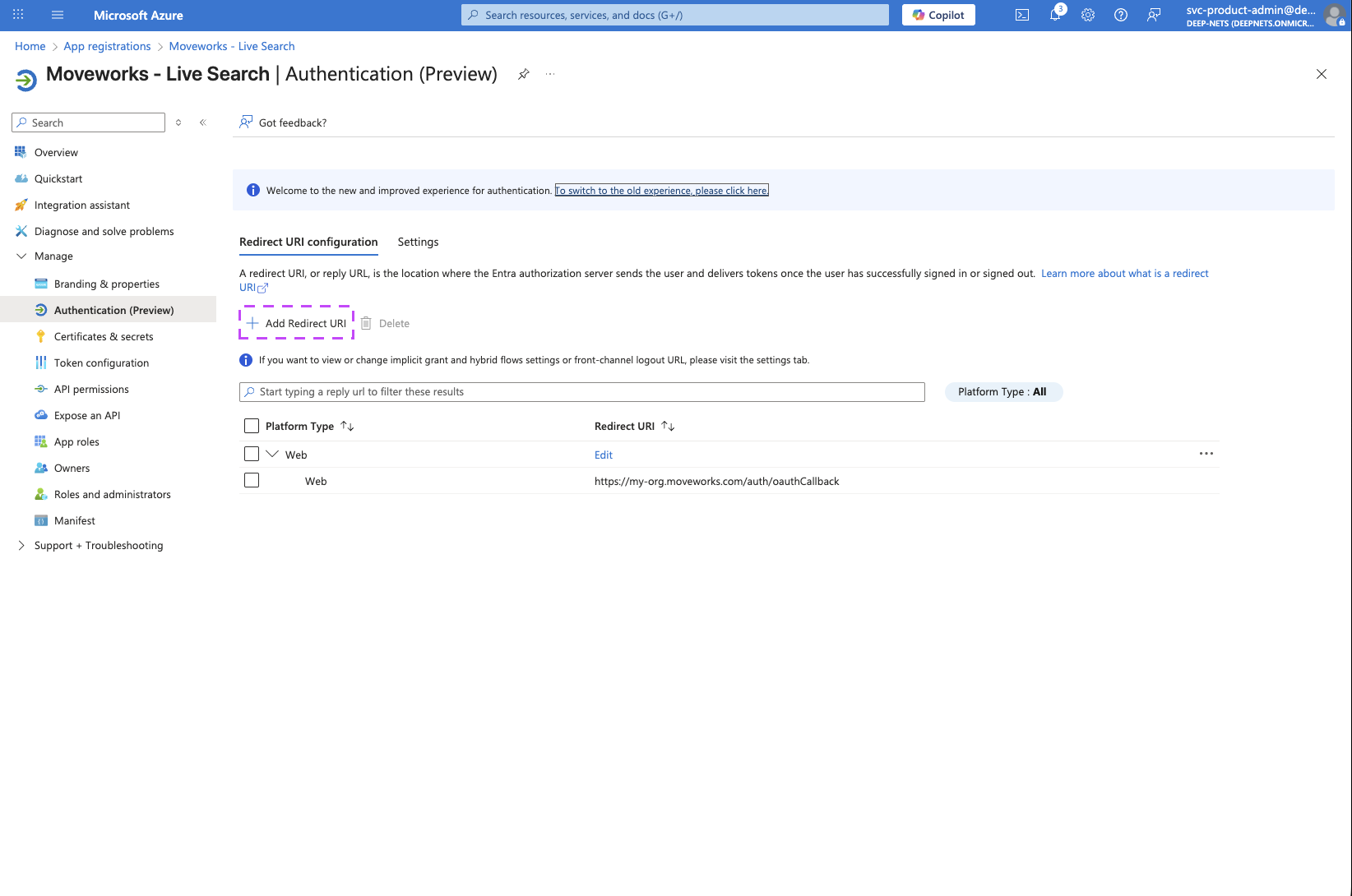
3. Select **Web**
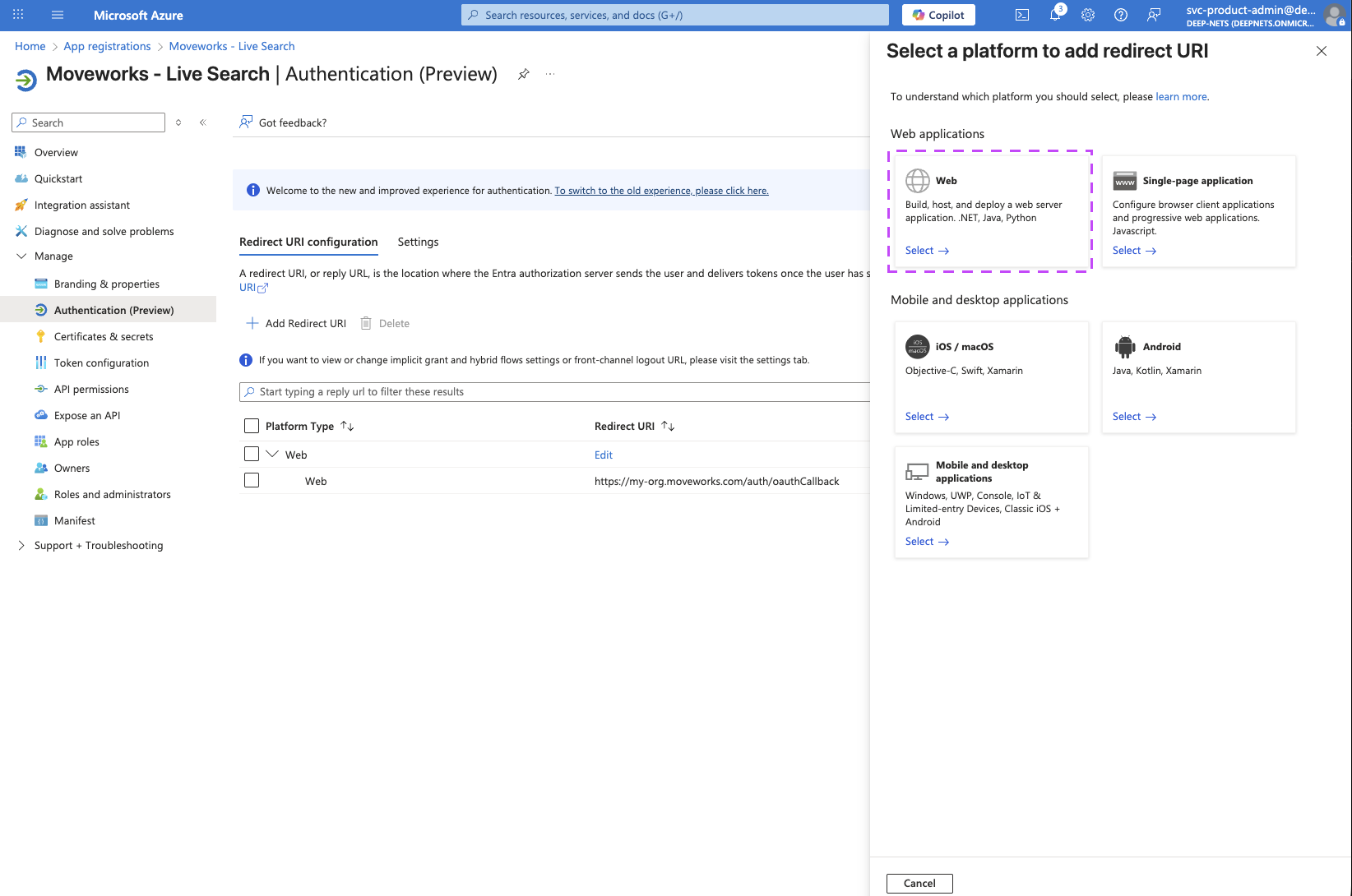
4. Enter the URL for your sandbox MyMoveworks environment and click on **Configure**.
> `https://{org}-sandbox.moveworks.com/auth/oauthCallback` — for US orgs
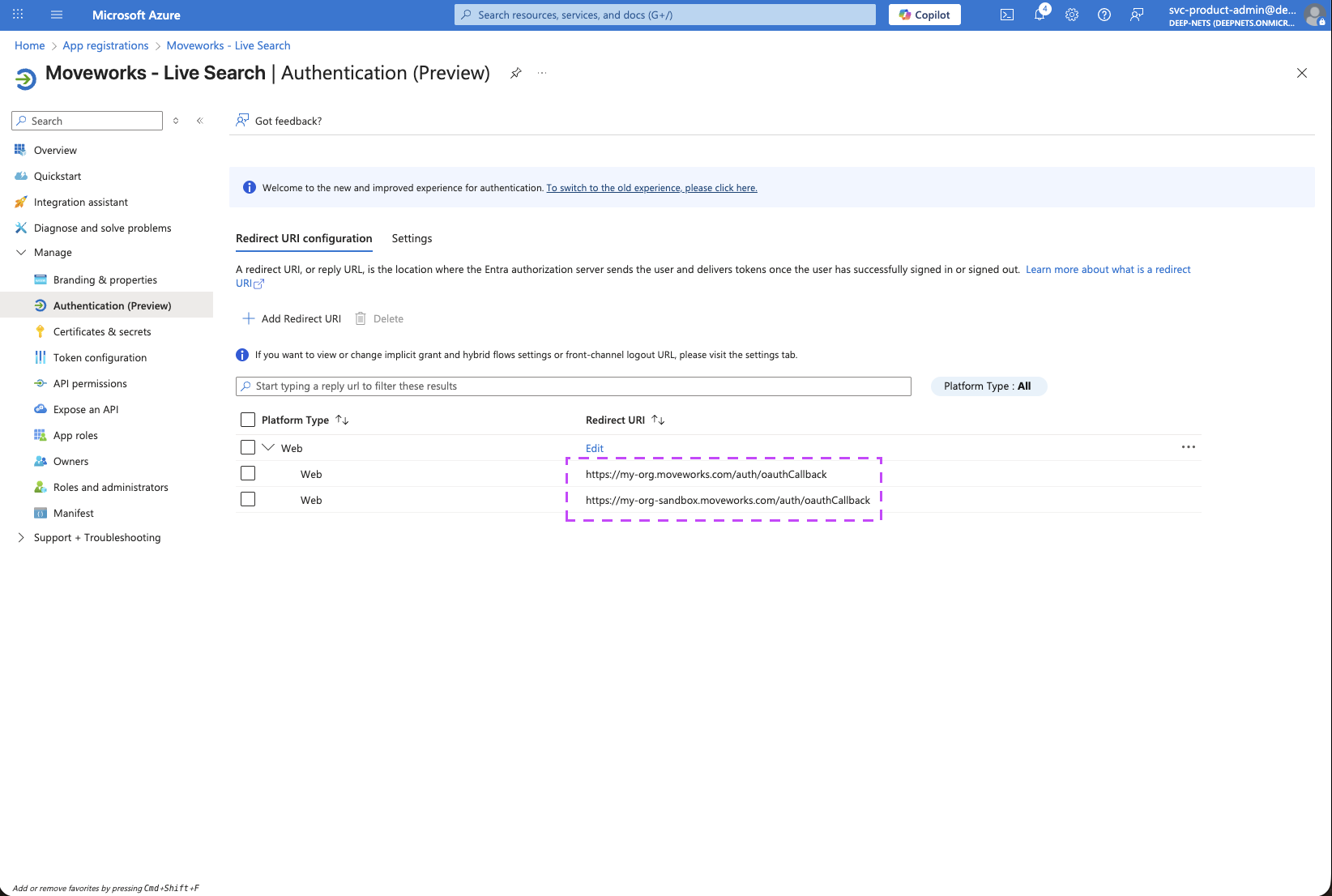
5. You should now notice both of your MyMoveworks URI configured on this page.
### 2. Setup API Permissions
1. Go to API Permissions to add the required MS Graph Permissions:
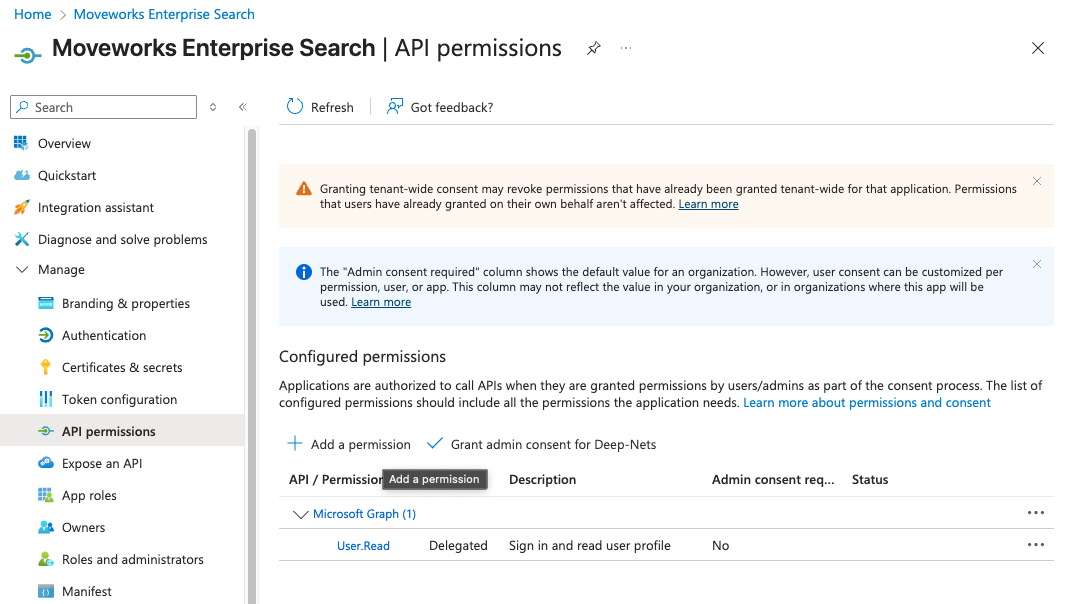
2. Click on **Add a permission** button. This will open a panel on the right side
3. Select **Microsoft Graph**.
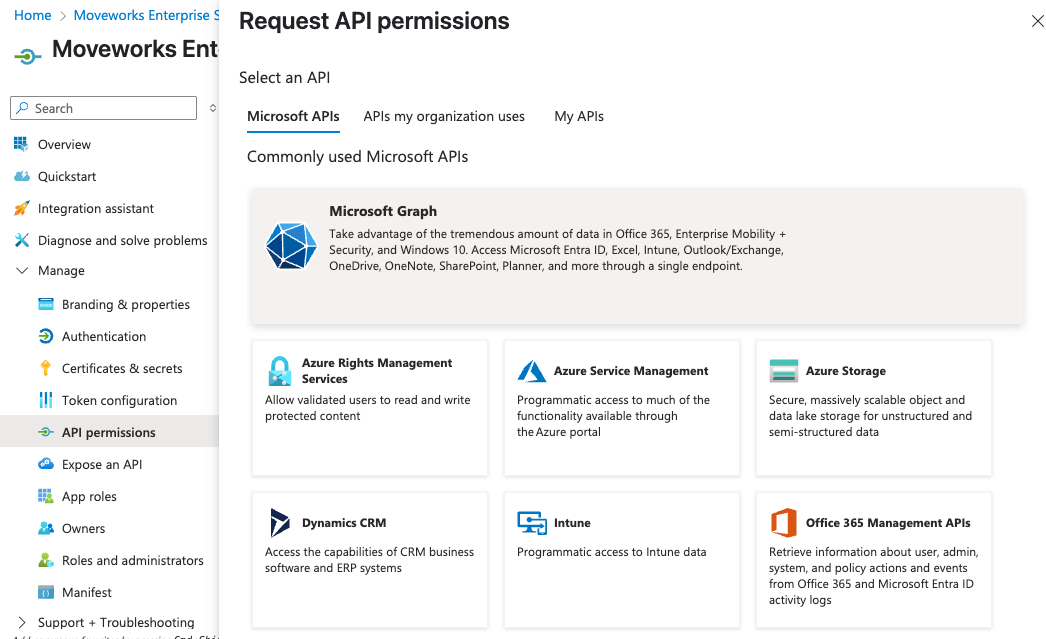
4. Choose **Delegated Permissions**.
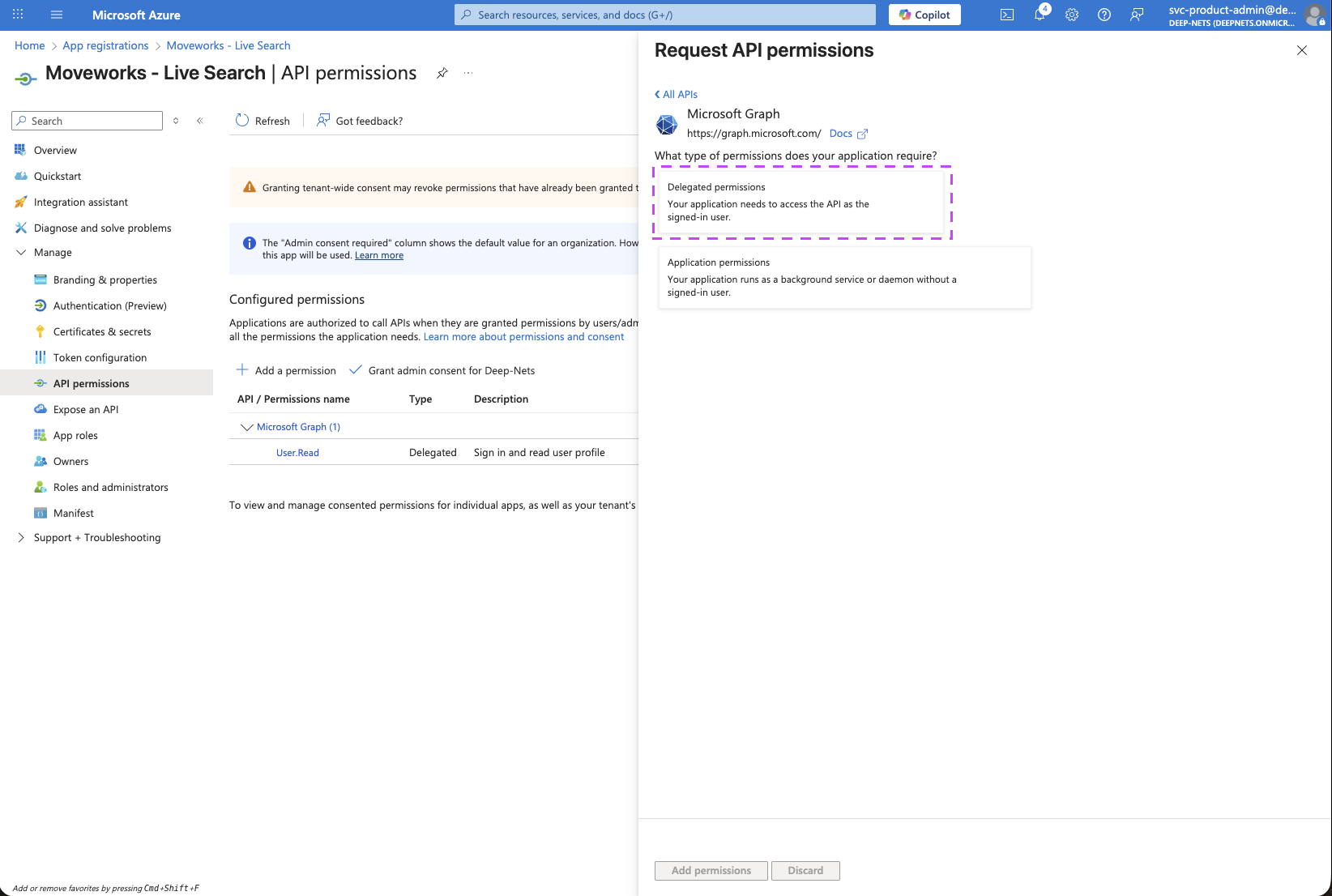
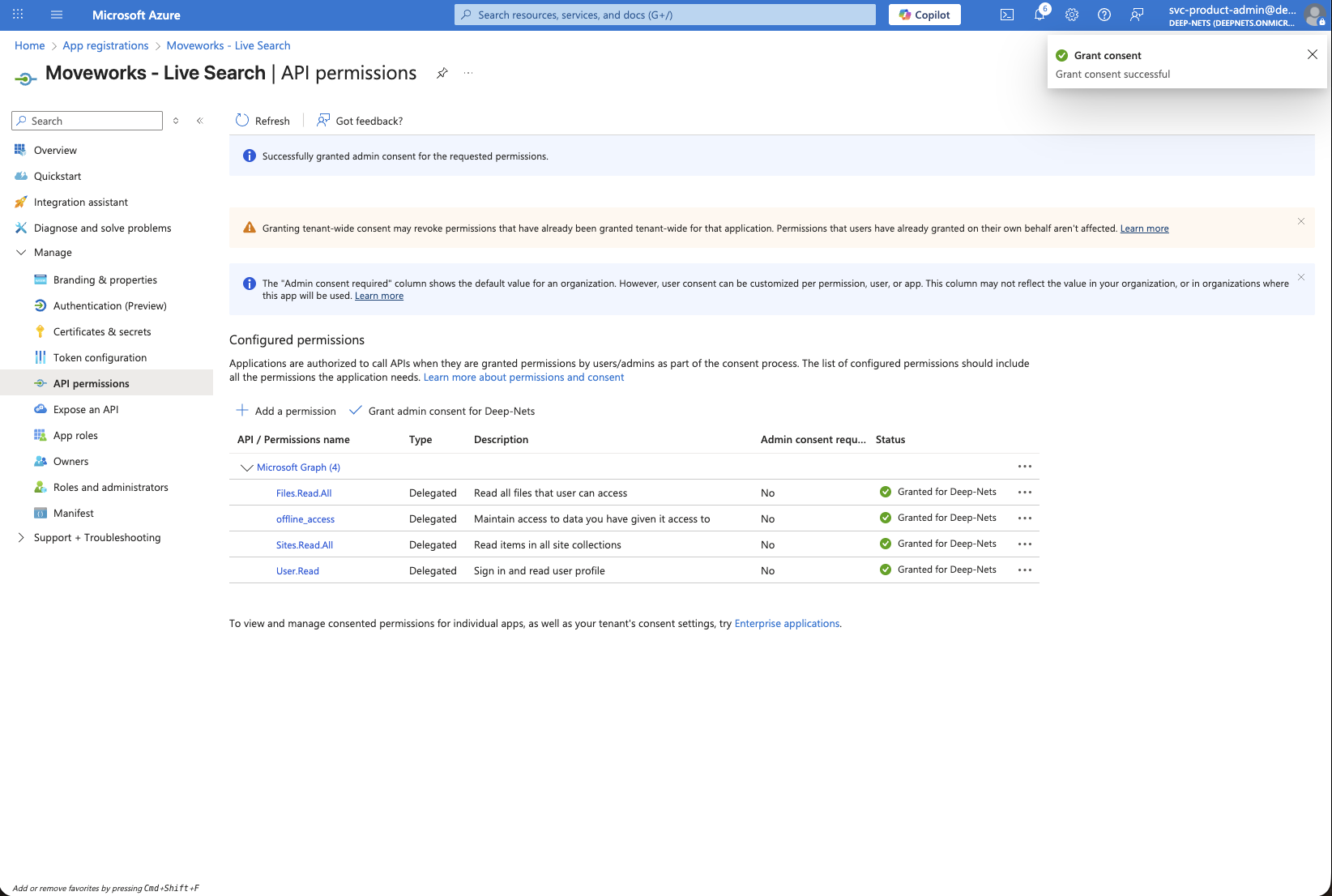
5. Ensure the following **Delegated Permissions** are added to the application.
1. `Files.Read.All`: lets Moveworks read files the user already has access to in OneDrive and SharePoint document libraries, so it can surface relevant results.
2. `Sites.Read.All`: lets Moveworks read site pages and list items the user can access in SharePoint Online.
3. `User.Read`: identifies the signed-in user.
4. `offline_access`: allows Moveworks to store a refresh token so the user doesn’t have to re-consent every time they search.
6. Click on Add permissions after selecting all of the above permission scopes.
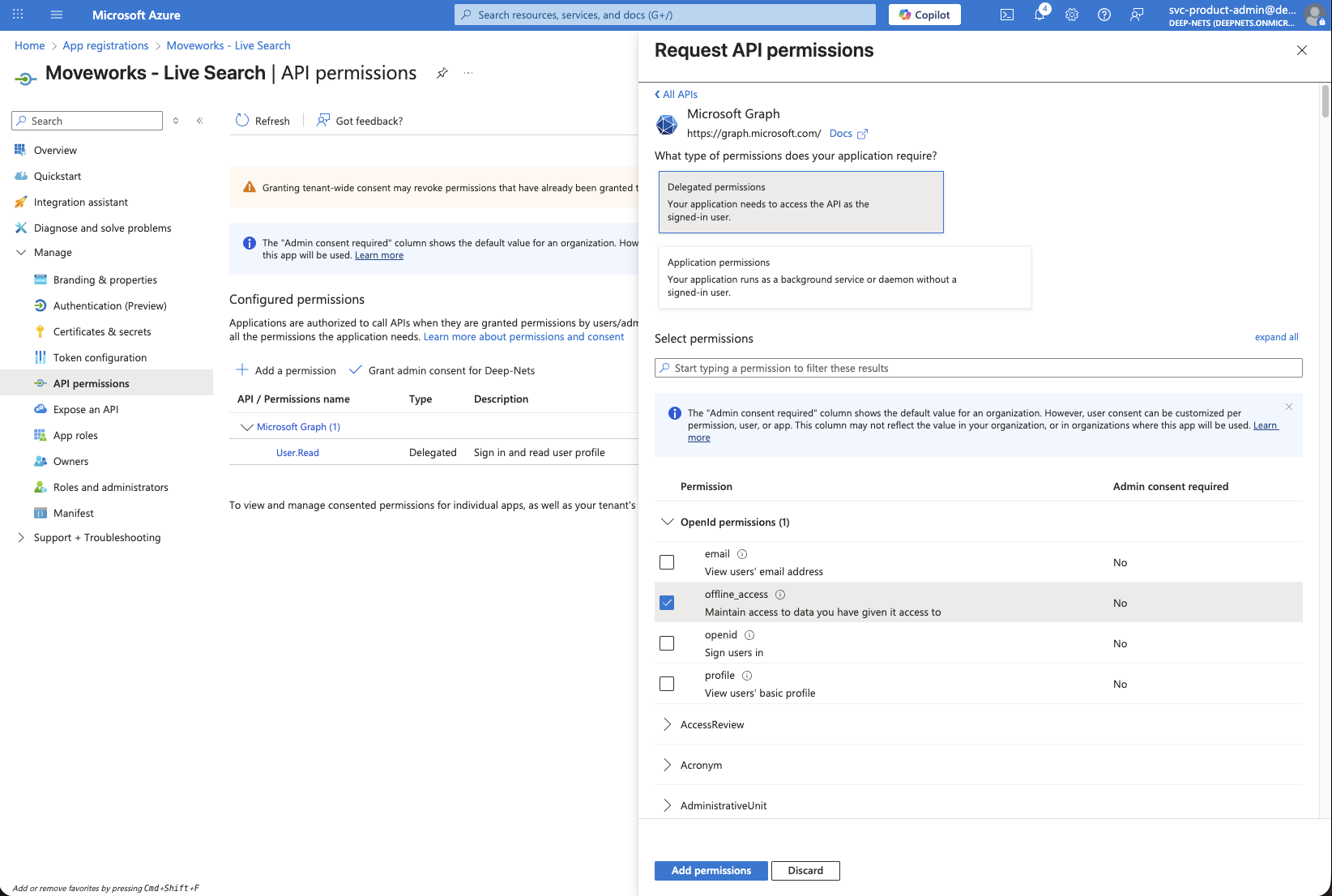
7. Verify that all 4 permission scopes are present under **Configured permissions**.
8. Click on the **Grant admin consent for your-org** button to make sure all permissions are available for all users to grant access.
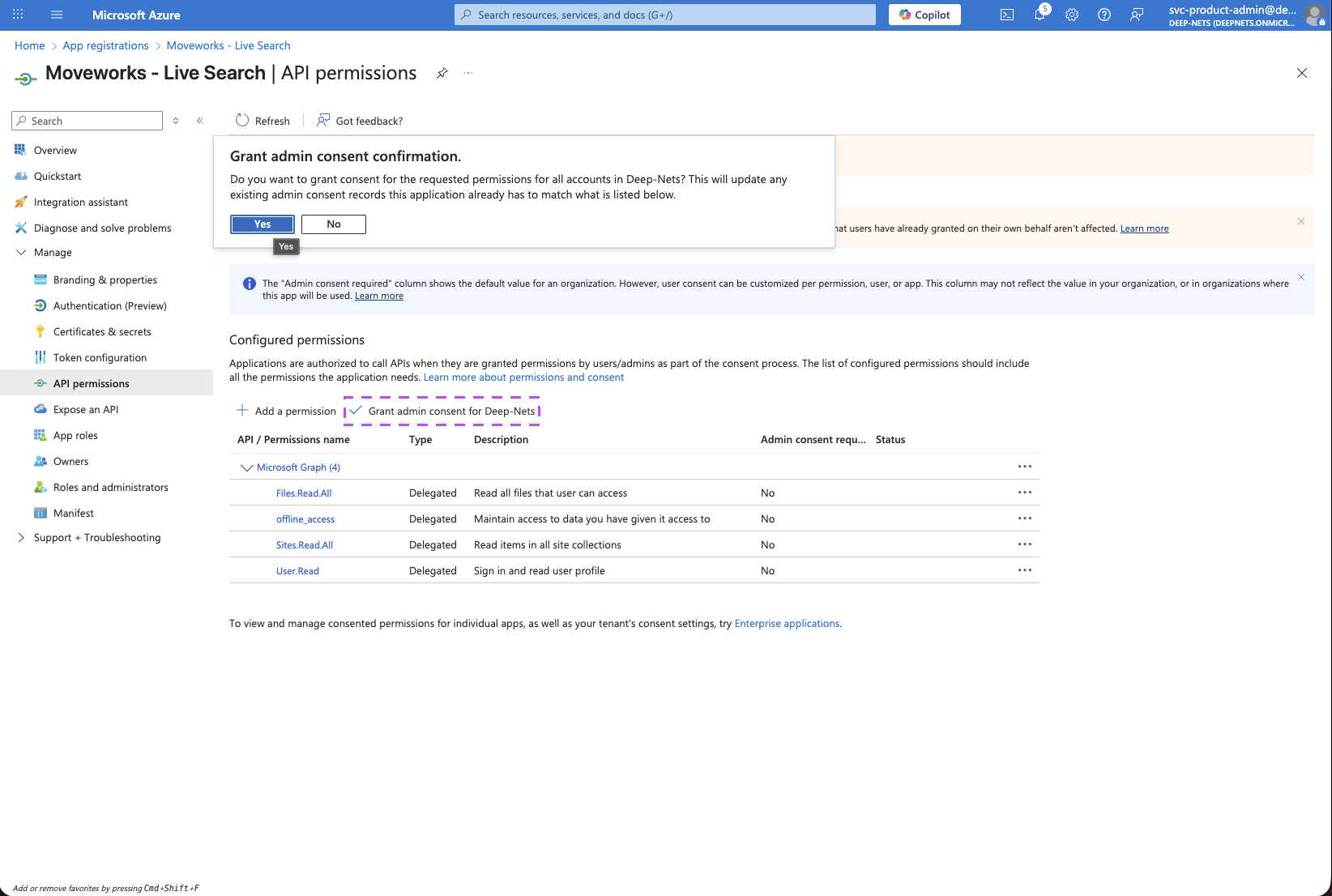
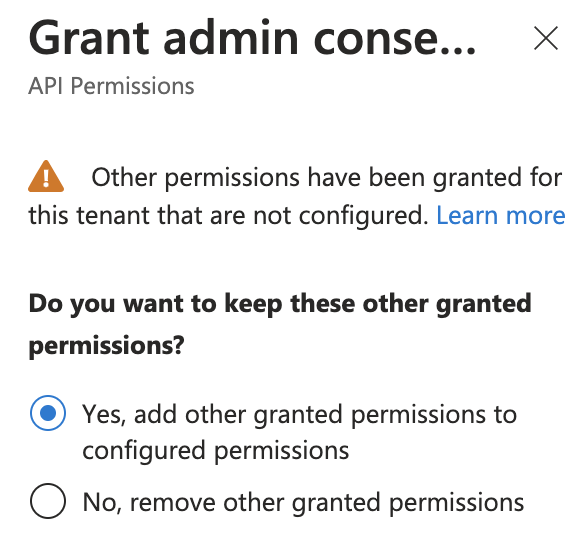
9. If this panel appears, click **Yes, add other granted permissions to configured permissions** then **Save and continue**, then **Grant admin consent,** and then **Yes**.
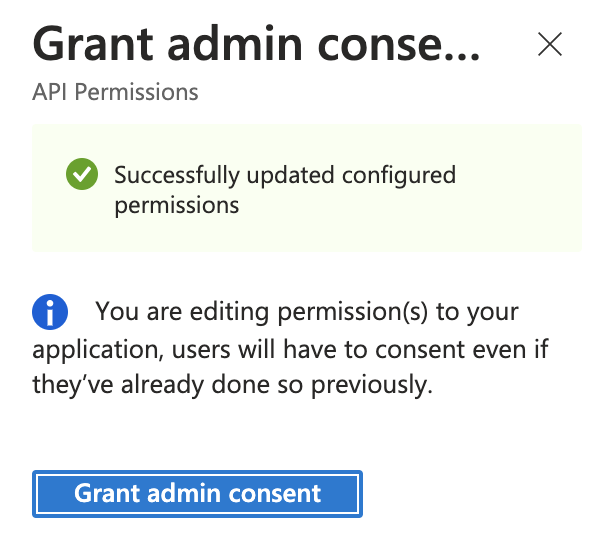
10. You will see green checkmarks on the newly added permissions if this was successful.
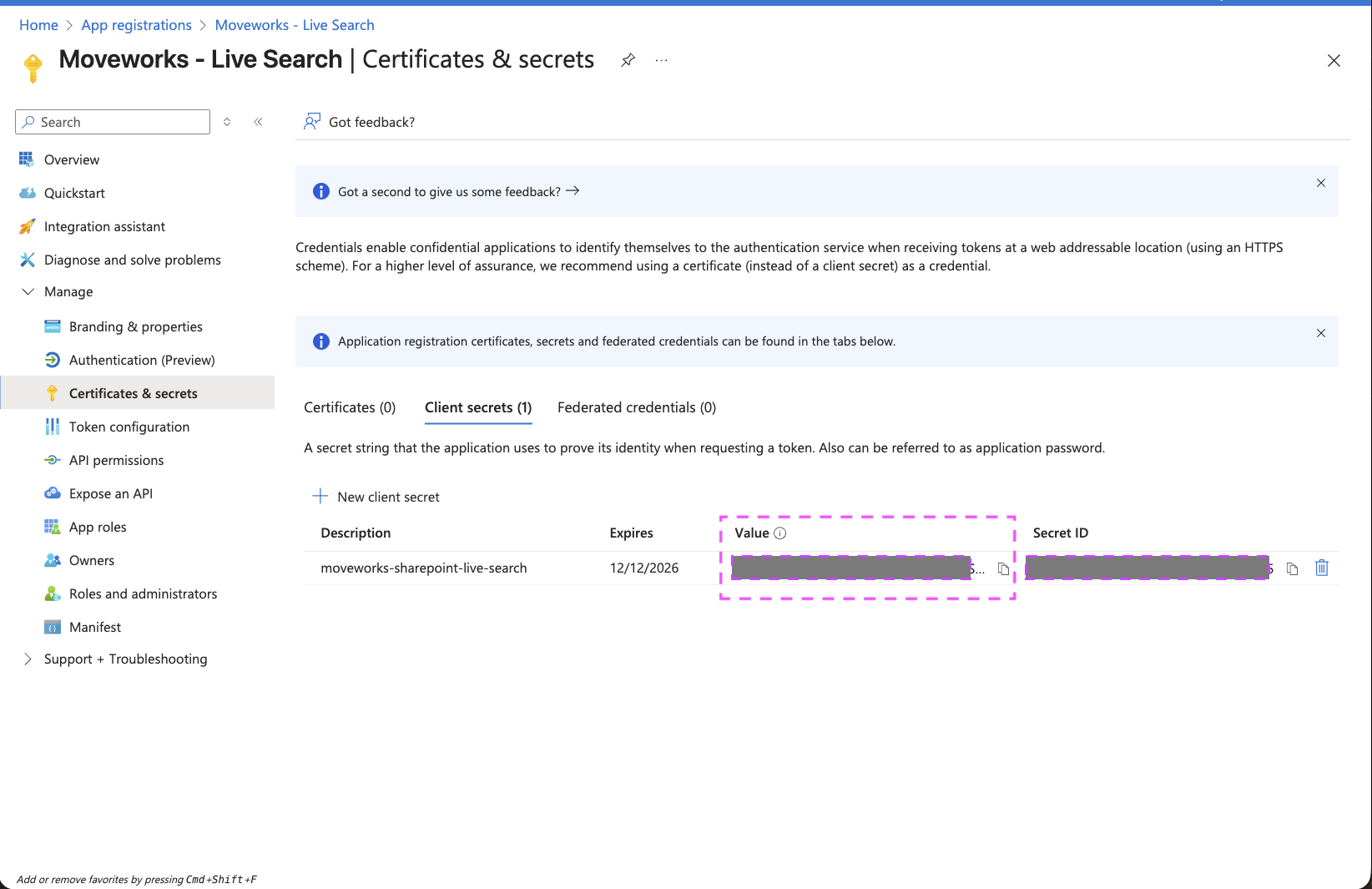
### 3. Generate Client Secret
Next, we will need to create a `Client Secret` for the Registration to connect it to Moveworks.
1. Navigate to the App you created above -> **Certifications & secrets**
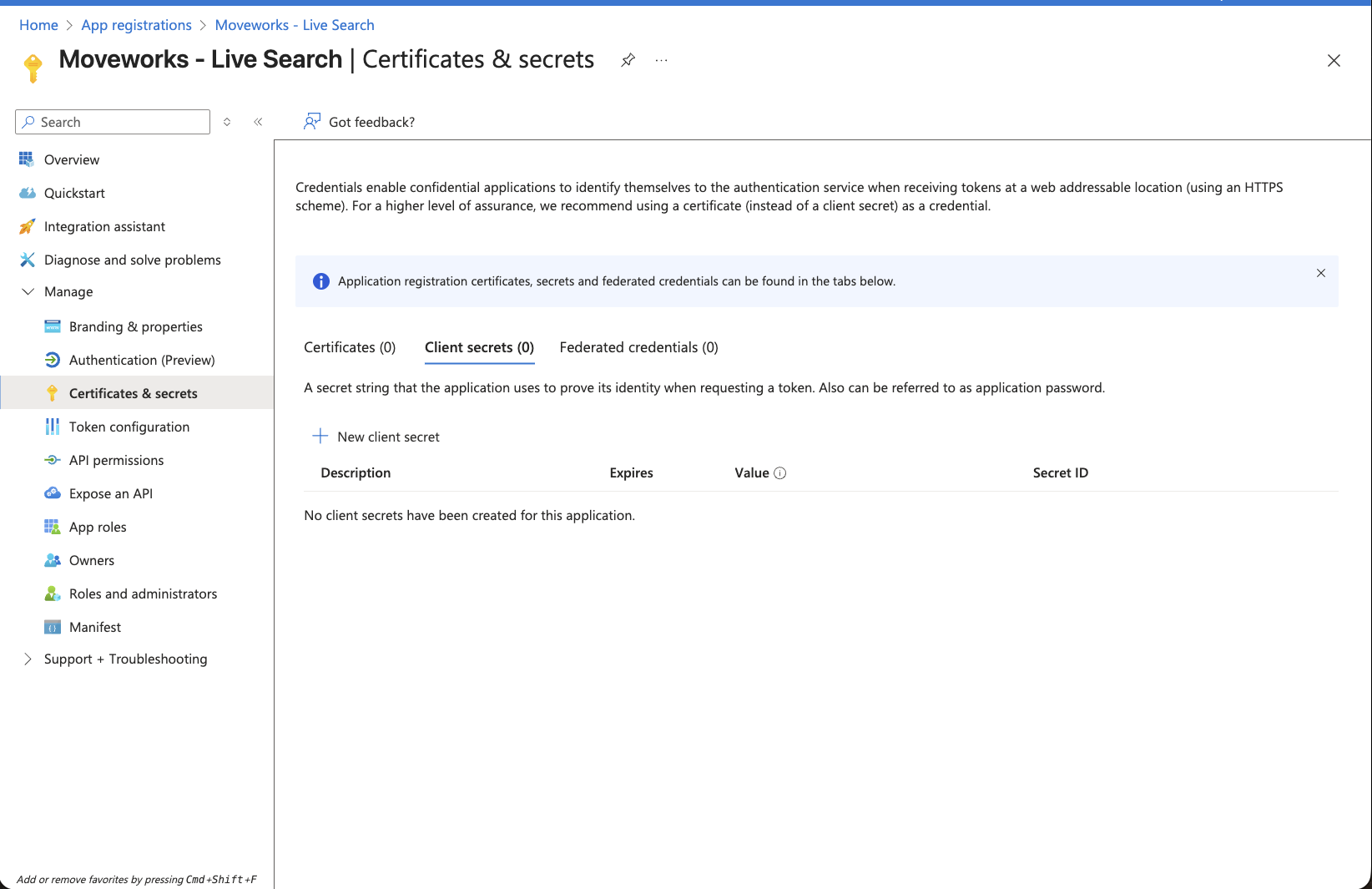
2. Click on New client secret button. This will open a panel on the right side.
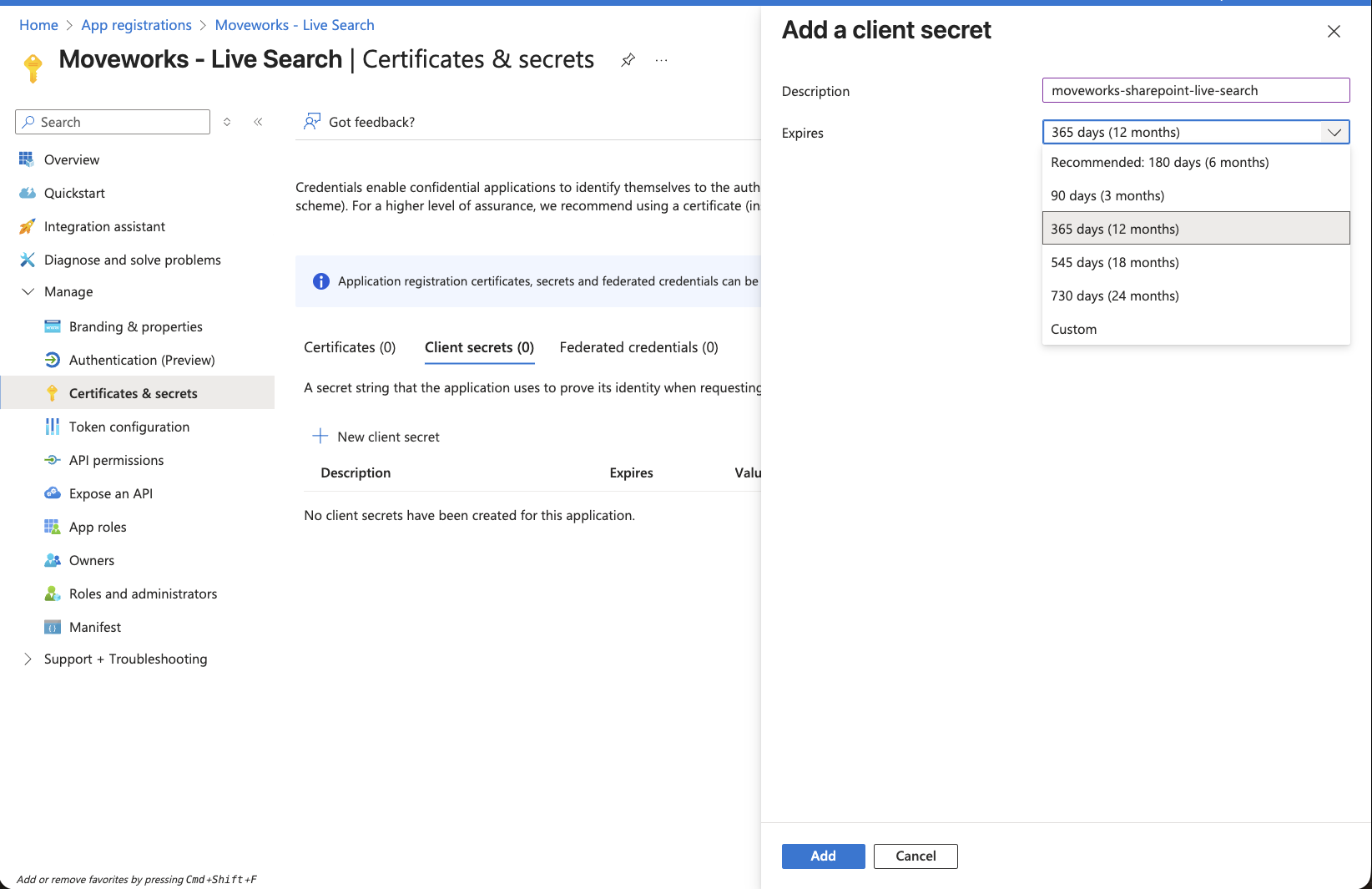
3. Set the description and expiry of this credential based on your org's policy and click on **Add**.
4. This will create a new entry on the **Client secrets** table
5. Make sure to copy the secret present in the **Value** column and store it in a secure location.
Note: Once you create the Secret, make sure to save it right now as it cannot be recovered later.
6. Go back to the **Overview** page, to capture the following details:
1. `Directory (tenant) ID`
2. `Application (client) ID`
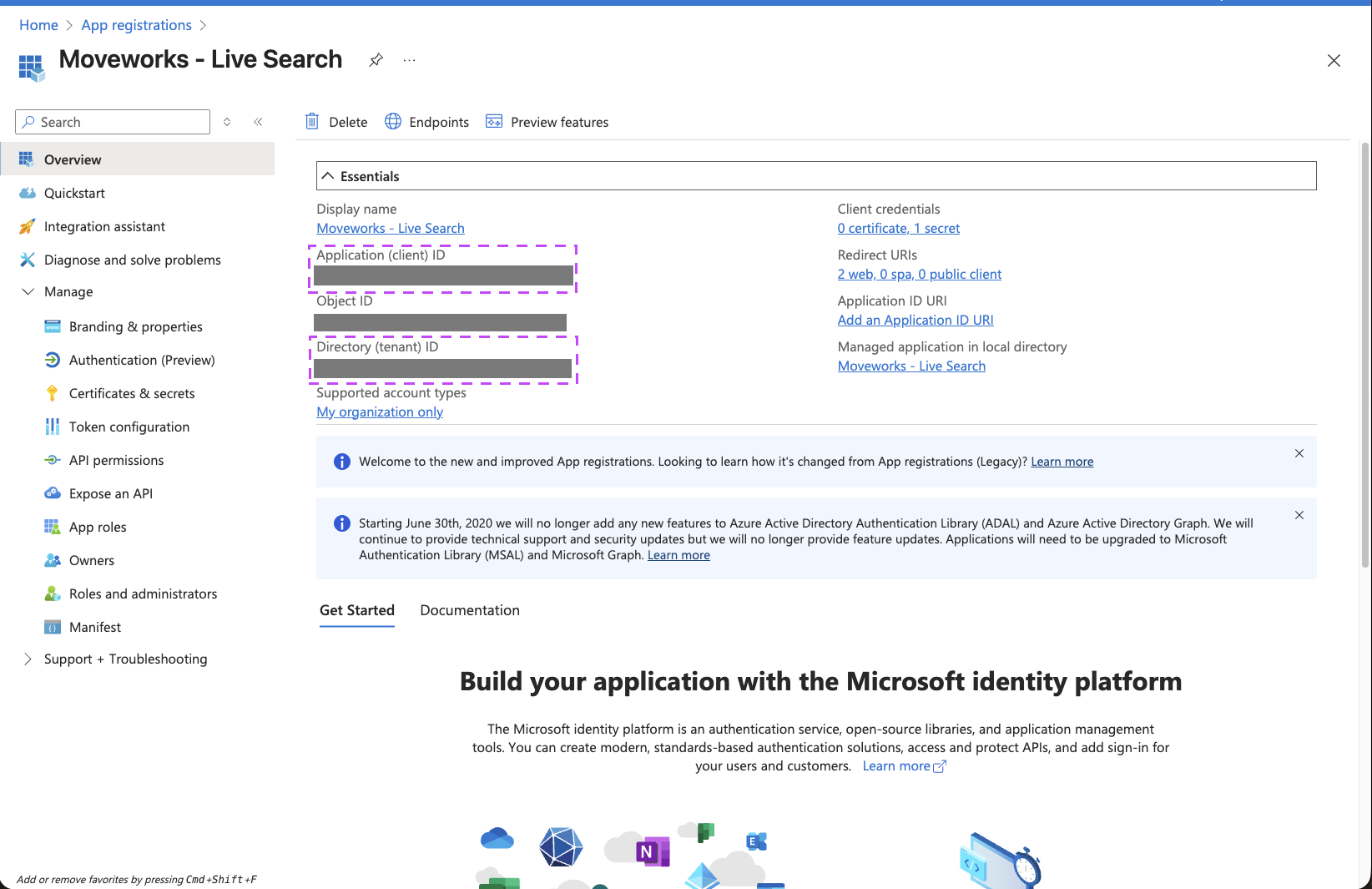
You have now completed all required steps to create a new Enterprise Application and generate the requisite credentials to setup a connector within Moveworks Setup for enabling Live Search. You should have the following details with you now:
* `Application (client) ID`
* `Directory (tenant) ID`
* `Client Secret`
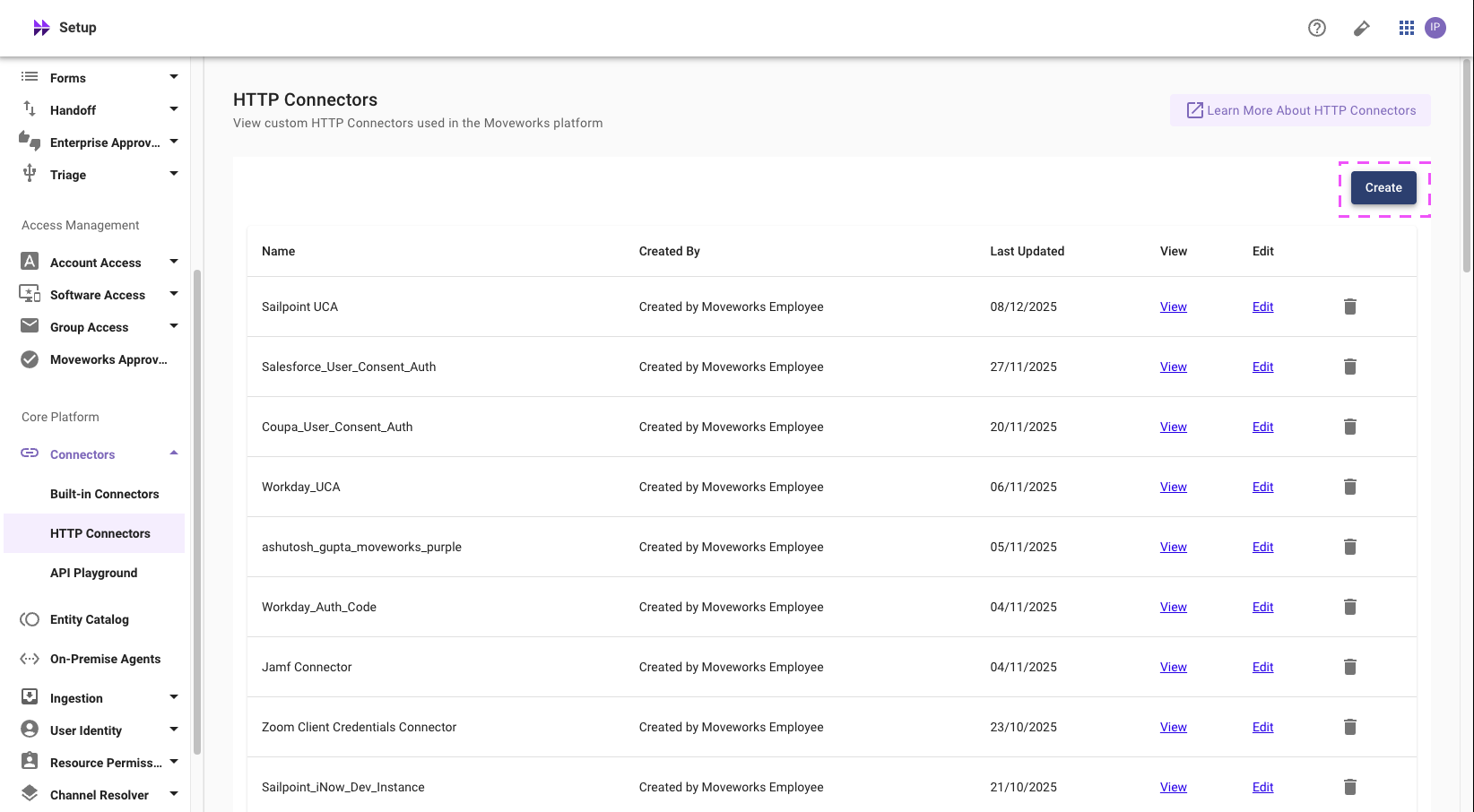
## Creating a new HTTP Connector in Moveworks Setup
Within Moveworks Setup, we need to create a new HTTP Connector to enable the connection, with the details from the previous step.
1. Head over to **Moveworks Setup > Core Platform > Connectors > HTTP Connectors**
2. Click on the **Create** button to create a new HTTP Connector
3. On this page, setup your Live Search connector based on the following parameters:
1. Connector Name: `enterprise_search_sharepoint_online`
2. Base URL — `https://graph.microsoft.com/`
3. Auth Config — `Oauth2`
4. Oauth2 Grant Type — `Authorization Code Grant`
5. Authorization URL — `https://login.microsoftonline.com/TENANT-ID-GOES-HERE/oauth2/v2.0/authorize`. Replace the tenant ID with the `Directory (tenant) ID` from the previous step
6. Client ID — The `Application (client) ID` from previous step
7. Client Secret — The `Client Secret` from previous step
8. Authorization Code Grant Scope — `offline_access User.Read Files.Read.All Sites.Read.All`
9. Authorization Request Query Parameters
1. `response_mode` | `query`
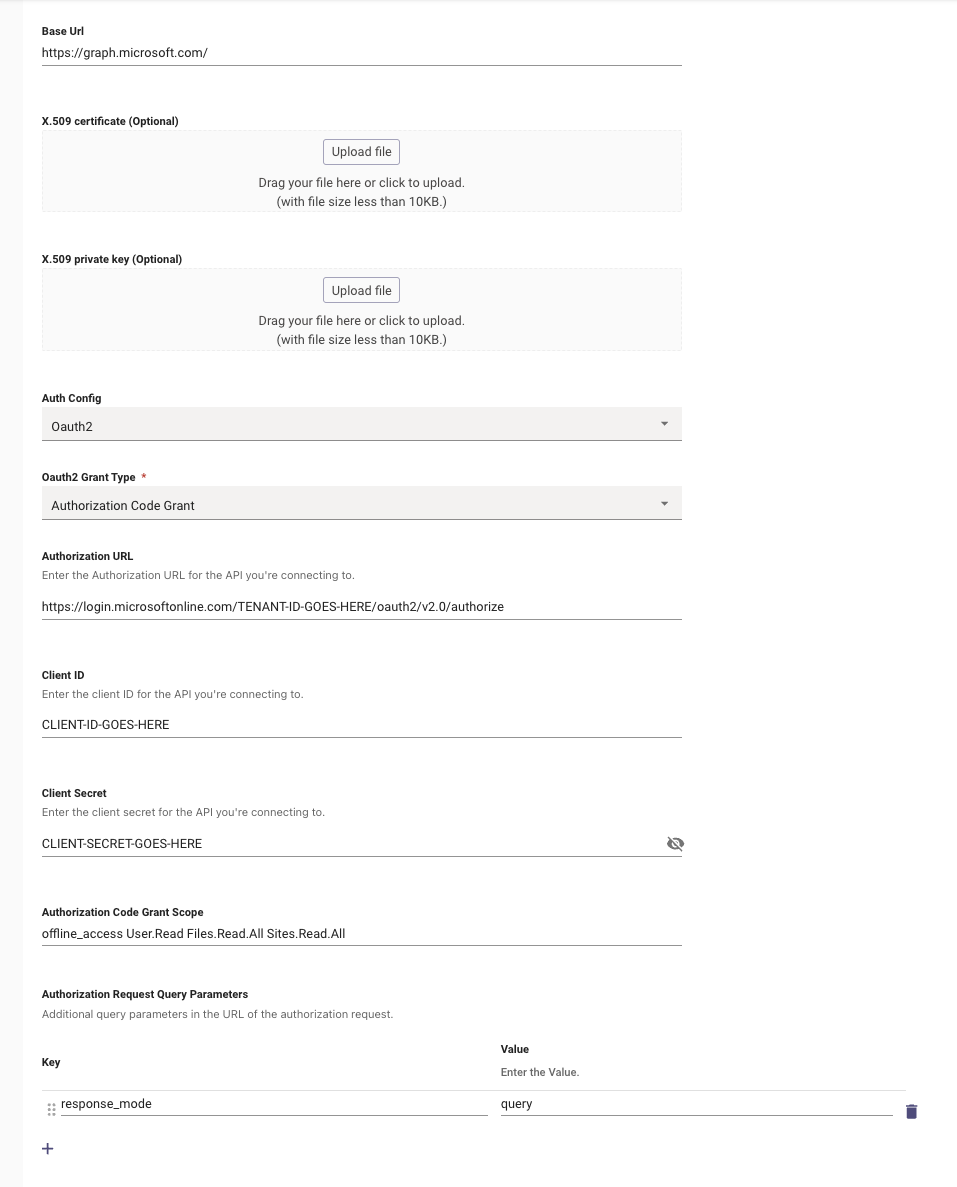
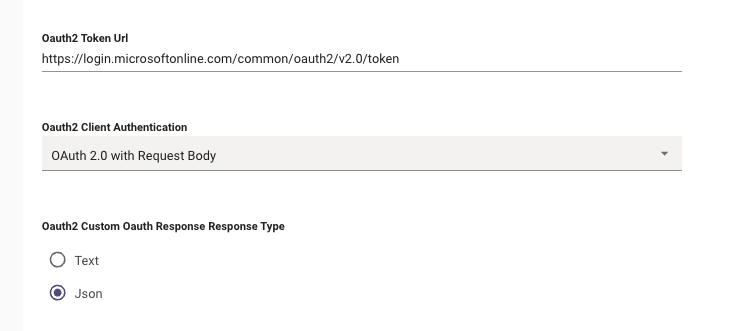
10. Lower on the connection configuration, add the token URL with the appropriate authentication type:
11. Oauth2 Token URL — `https://login.microsoftonline.com/TENANT-ID-GOES-HERE/oauth2/v2.0/token`
12. Oauth2 Client Authentication — `OAuth 2.0 with Request Body`
Once this connector is saved, please notify the Moveworks team. We’ll complete the remaining Live Search configuration and validate SharePoint & OneDrive search end-to-end.